China-based Supply Chain Cyberattacks Hit Thousands of Android

Daily Cyber and Tech Digest, ASPI Cyber, Tech & Security

Flawed by Design: Electronics with Pre-Installed Malware – Georgetown Security Studies Review
Iran-Run ISP 'Cloudzy' Caught Supporting Nation-State APTs, Cybercrime Hacking Groups - SecurityWeek

SmugX: Chinese APT uses HTML smuggling to target European Ministries and embassies
300+ Terrifying Cybercrime & Cybersecurity Statistics (2024)

China-based Supply Chain Cyberattacks Hit Thousands of Android Devices

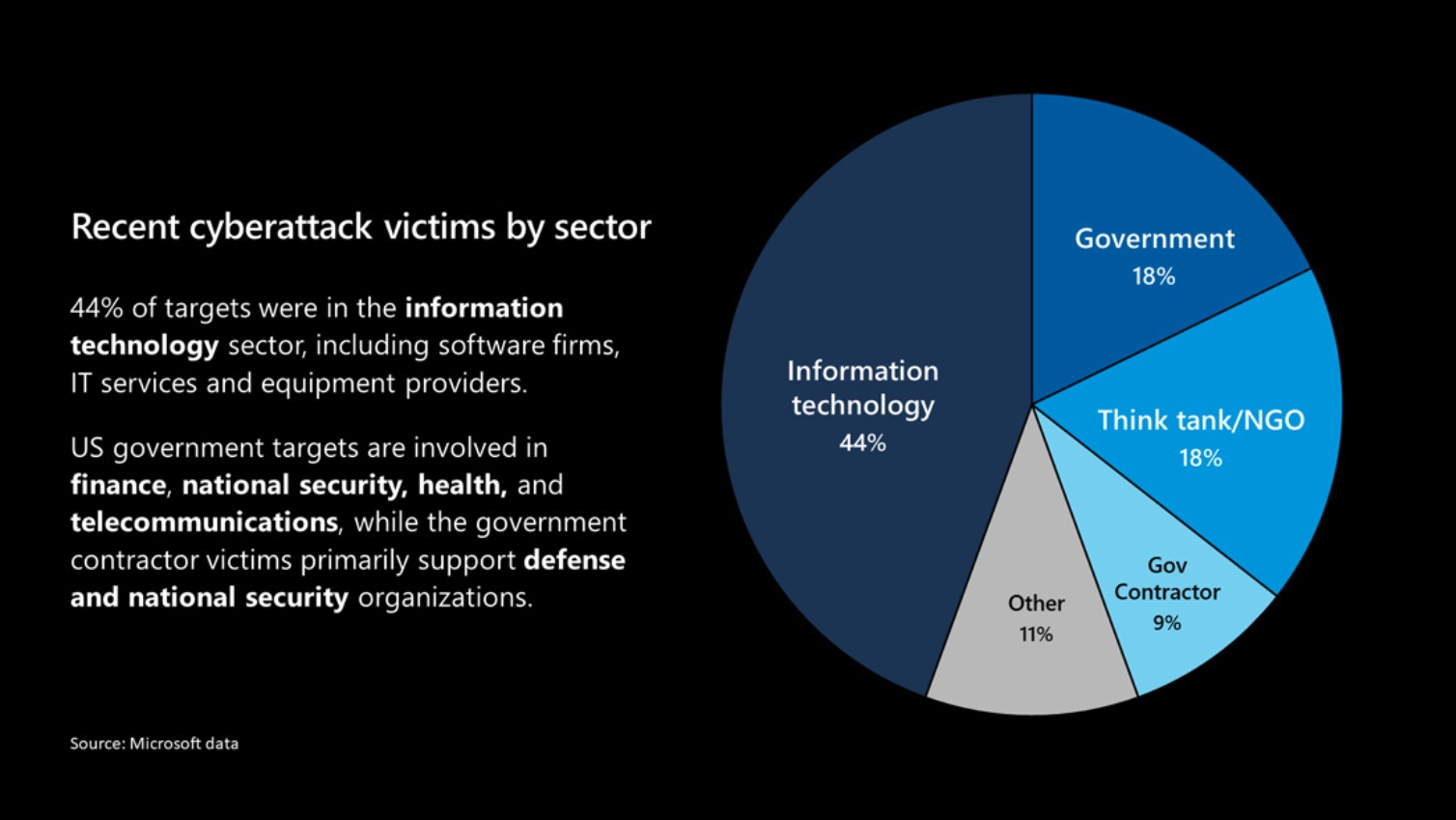
Supply Chain Attacks: A Growing Threat
SolarWinds & Accellion Breaches: Supply Chain Attacks Wreaking Havoc - Security Boulevard
Tracing the Supply Chain Attack on Android – Krebs on Security
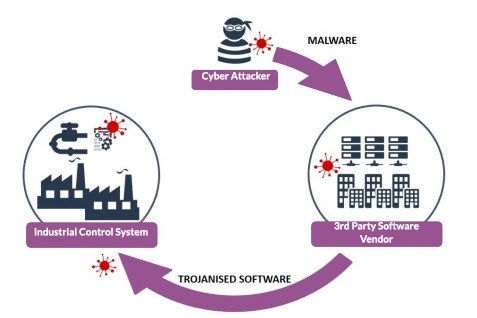
Supply Chain Attacks and their impact on OT/ICS Cybersecurity
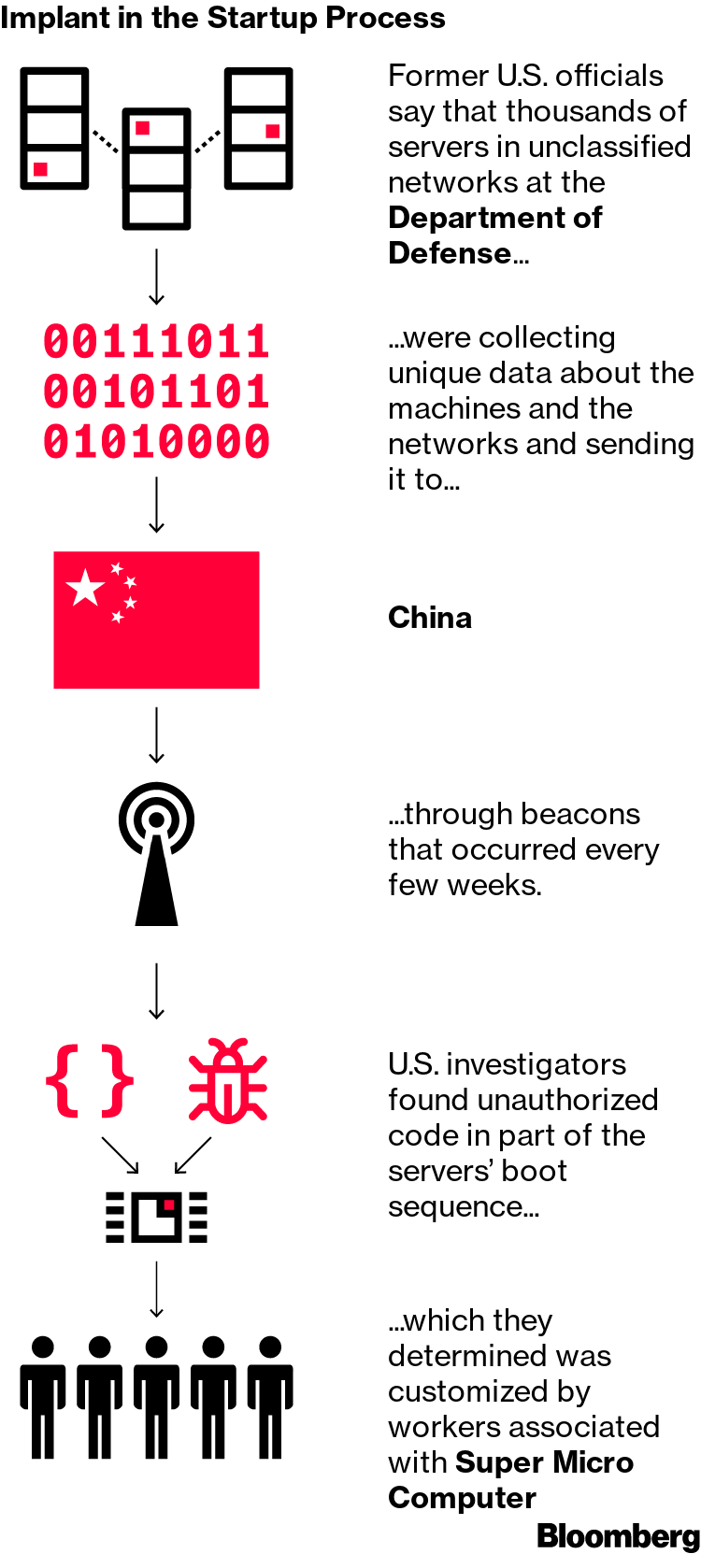
Supermicro Hack: How China Exploited a U.S. Tech Supplier Over Years
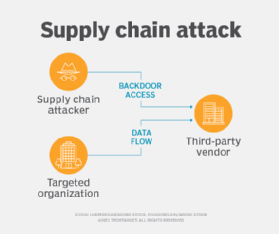
What is a Supply Chain Attack?